A key fact to know about network penetration testing for beginners: If an organization pays someone to try to break into its network, it typically wants that person to... Read more »

The saying, “If it isn’t broken, don’t fix it,” doesn’t necessarily line up with the idea of network penetration testing, where a tester breaks into something typically to fix... Read more »

Organizations of all sizes have adopted cloud strategies to varying degrees. While beneficial in many ways, the cloud also has its risks, which organizations should fully assess before placing... Read more »

The average time to detect and contain a data breach is 280 days, according to IBM’s “2020 Cost of a Data Breach Report.” This makes clear that monitoring IT... Read more »
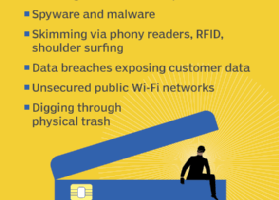
Given the exponential growth of e-commerce and online transactions, cybersecurity has never been more critical. Hackers may attempt to invade our privacy in several ways, but one area they... Read more »
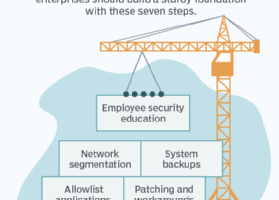
Without a strong network security strategy, IT security will fall short — and vice versa. The National Security Agency (NSA) has identified three basic functions to form the foundation... Read more »
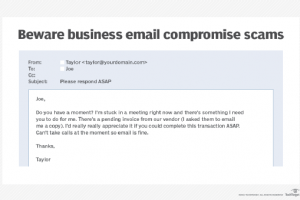
“Please respond ASAP.” When CFO Joe receives an email from CEO Taylor with this urgent subject line, he goes into high alert. The message is pressing. The email’s sender,... Read more »
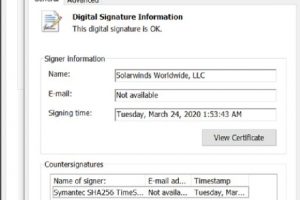
2020 was a roller coaster of major, world-shaking events. We all couldn’t wait for the year to end. But just as the 2020 was about to close, it pulled... Read more »
The majority of malware infections begin with a phishing email. These simple lures, which trick recipients into opening malicious attachments or clicking links that lead to malicious web content,... Read more »
Forensics teams are still investigating how hackers were able to exploit SolarWinds’ patching system to attack numerous high-profile commercial and governmental organizations, including Microsoft and the U.S. Department of... Read more »